Overview
Easycrack is a Windows x86-64 binary designed to reverse and find the password hash.
For this challenge, I will be using IDA Free 9.2
Initial Recon
Running the binary prompts the user to enter a password
Program prompt requesting password
Static Analysis
We load the binary into IDA for inspection.
In the main function we search for the “Password incorrect” text by pressing Alt + T.
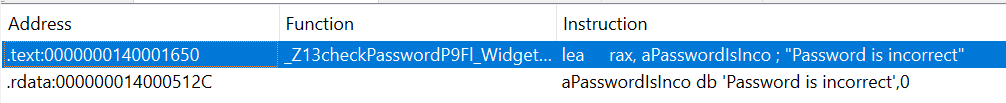
Search string
Double click the first occurrence and change from graph view to text view.
Search string
Hmmm, that looks interesting lets list its cross references.
Since there is only one cross reference lets follow that.
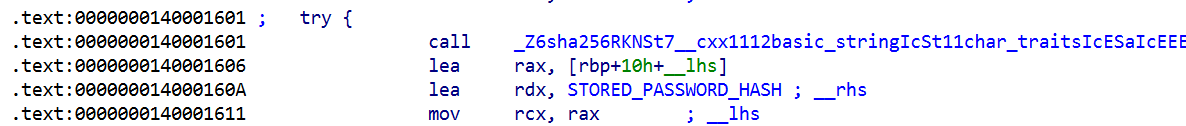
Lets list cross references to it again.
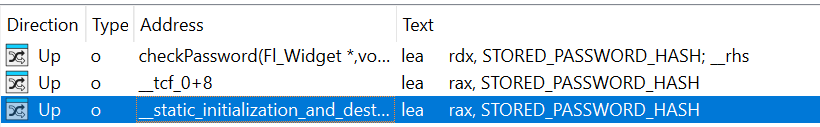
Search string
Interesting, lets investigate the reference that says “initialization”.
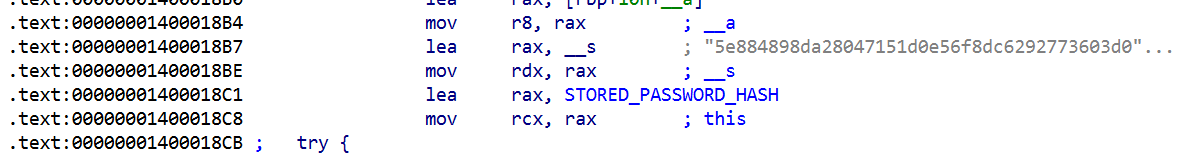
Initialization function
Great!! It looks lik it is storing a hash into a variable, lets decompile this!
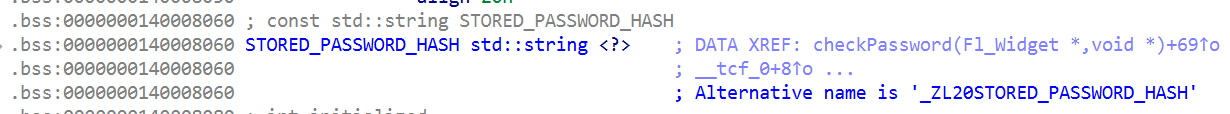
5e884898da28047151d0e56f8dc6292773603d0d6aabbdd62a11ef721d1542d8
Look at that hash!! lets identify what hash algorithm is this
I’ll be using THIS SITE
5e884898da28047151d0e56f8dc6292773603d0d6aabbdd62a11ef721d1542d8:password:SHA256X1PLAIN
Amazing we have our hash broken and the password is “password” weird but it is what it is.
Lets use that when the program asks for the password.
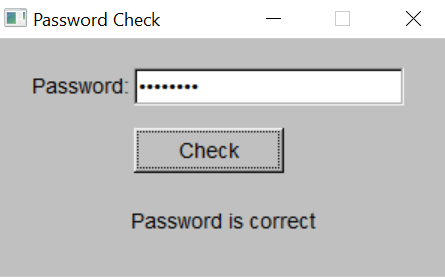
Final validation
Exellent, we found it!!
Conclusion
Objective: Recover the password from a Windows x86-64 binary.
Approach:
- Used IDA Free 9.2 for static analysis
- Traced the “Password incorrect” string to its references
- Followed cross-references to locate the stored hash
- Identified the hash as SHA-256 and recovered the plaintext
Key Insight
Even when not immediately obvious, following strings and cross-references systematically can uncover hardcoded secrets within a binary.